ISMS App: Pragmatic Information Security Management for Mid-Market Companies

Photo: Tima Miroshnichenko / Pexels
The Challenge: Introducing ISMS Without Overcomplicating It
An established automotive supplier faced a familiar dilemma: VDA compliance required structured information security according to ISA/Basis standards. Yet it was clear that heavyweight ISMS tools like Verinice or HiScout didn't fit the company culture. What was needed was a pragmatic approach—one that presented security not as a compliance burden, but as an integrated business process.
The requirements were multifaceted: centralized management of information assets with classification, mapping to applications and business processes, automated risk analysis based on standardized threat catalogs, and a solution that integrates seamlessly into the existing Microsoft 365 ecosystem. Traditional ISMS software felt too rigid and too expensive for the company's actual needs.
The Solution: ISMS App on Microsoft Dataverse
The project team chose to build a purpose-built ISMS app using Microsoft Dataverse and Power Platform Model-Driven Apps. This decision unlocked several advantages: the solution leverages existing Microsoft 365 licenses, scales flexibly as the organization grows, and can be extended iteratively without wholesale replacement.
The app implements the proven VIVA principle for protection requirement assessment. VIVA stands for Vertraulichkeit (Confidentiality), Integrität (Integrity), Verfügbarkeit (Availability), and Authentizität (Authenticity)—the four pillars of modern information security. Every information asset is systematically classified according to these criteria. This classification then cascades to all associated applications and business processes, automatically determining the protection requirements for each process and IT system.
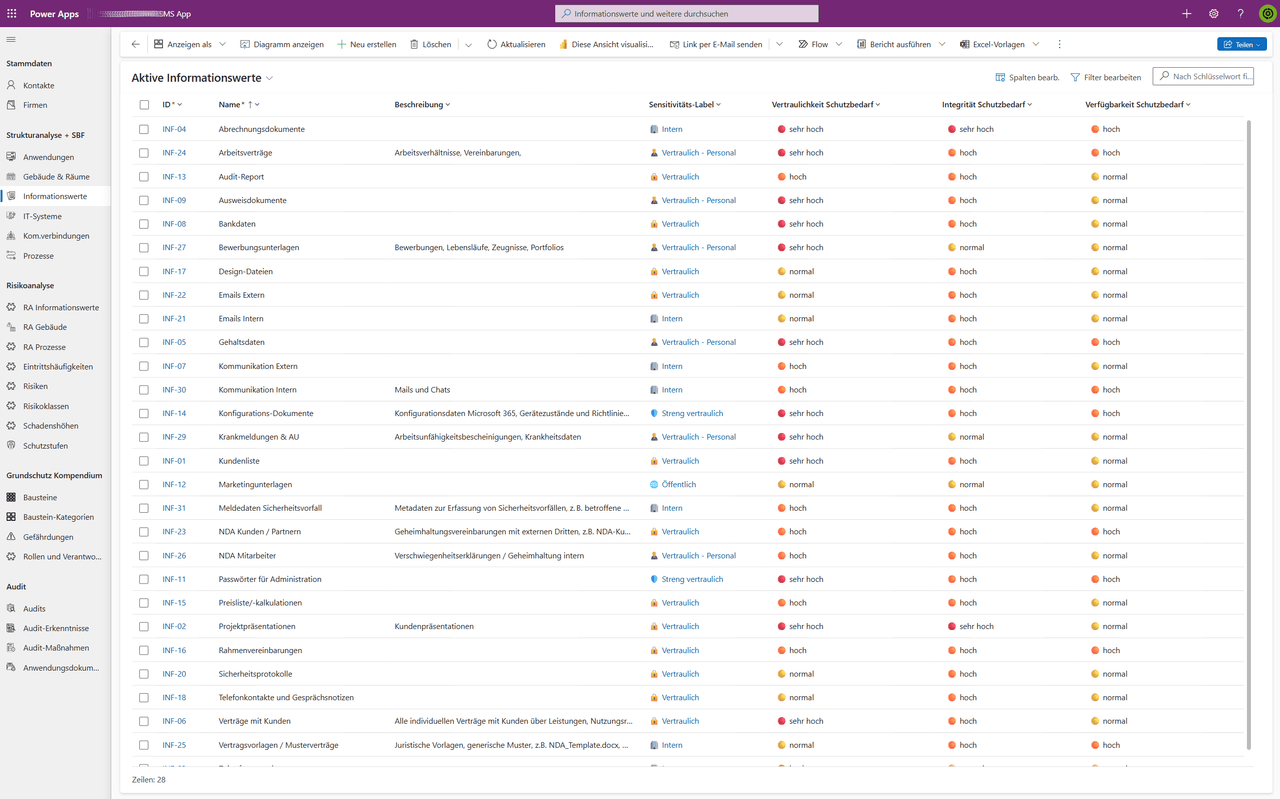 Central capture of information assets with VIVA classification forms the foundation for automated protection requirement inheritance
Central capture of information assets with VIVA classification forms the foundation for automated protection requirement inheritance
Automated Risk Analysis and Standardized Risk Catalog
The heart of the app is a comprehensive risk catalog containing over 70 standardized risks directly mapped to the BSI control framework (BSI 200-3). This is crucial: rather than requiring analysts to identify risks from scratch, the app presents industry-specific and technology-specific risks in a structured format. This accelerates risk analysis while ensuring that commonly overlooked threats don't slip through the cracks.
The risk analysis itself follows a pragmatic two-step approach: for each relevant risk, analysts enter the probability of occurrence and potential impact. The app automatically calculates the risk class from this combination. To simplify visualization, the app uses color-coded choice fields: green for acceptable, yellow for tolerable with controls, red for critical. This visual approach makes risk landscapes immediately comprehensible and supports prioritization of remediation measures.
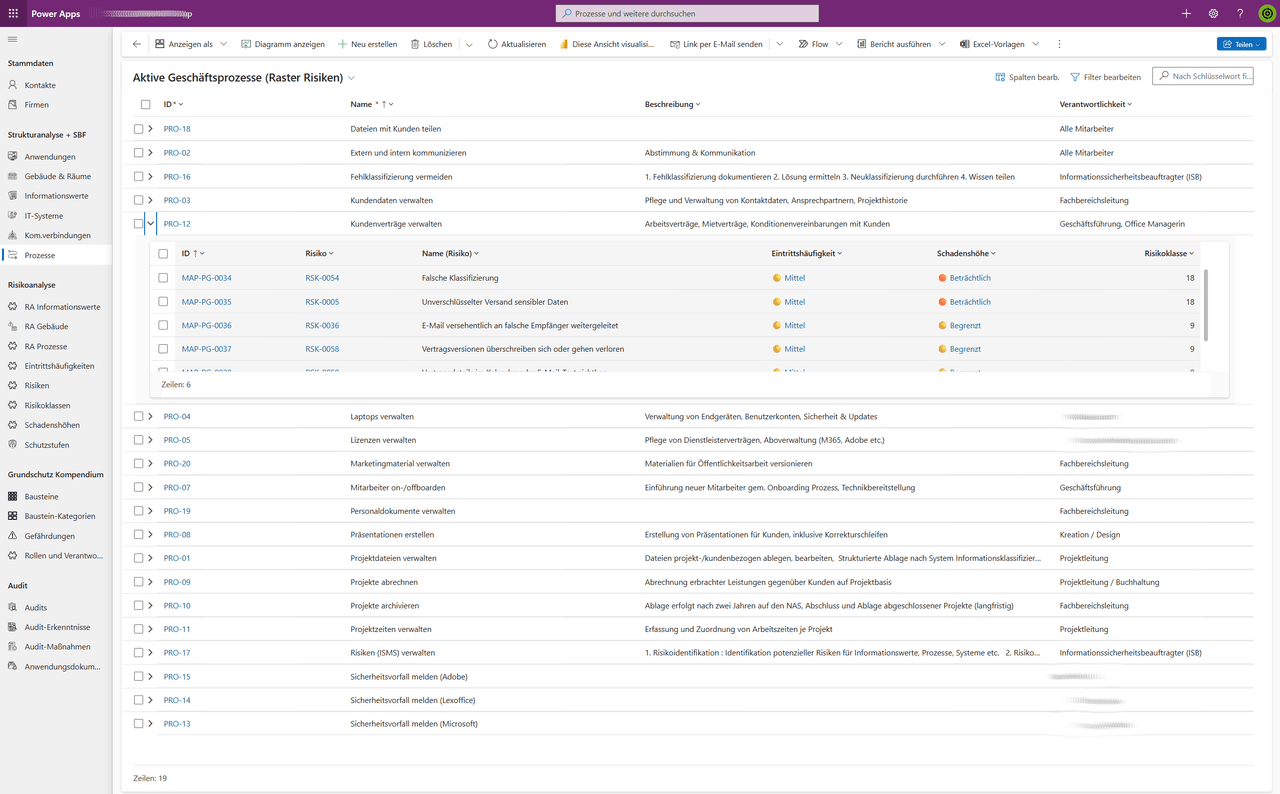 The risk catalog combines standardized threats with custom frequency and impact ratings, automatically calculating risk classes
The risk catalog combines standardized threats with custom frequency and impact ratings, automatically calculating risk classes
Mapping and Modularity: From Applications to Vulnerabilities
The app enables complex many-to-many relationships through mapping tables. A single information asset can be processed through multiple applications. One application can serve multiple business processes. A process can depend on multiple IT systems. This flexibility is fundamental for realistic security modeling: in complex organizations, these interconnections are the norm, not the exception.
The ISMS app covers all central modules of a modern security management system: information assets (with VIVA classification), business processes, IT systems (rooms, computers, networks), applications, communication links, vulnerabilities, and controls. This modular structure means the system can evolve over time—new modeling concepts can be added without disrupting the existing foundation.
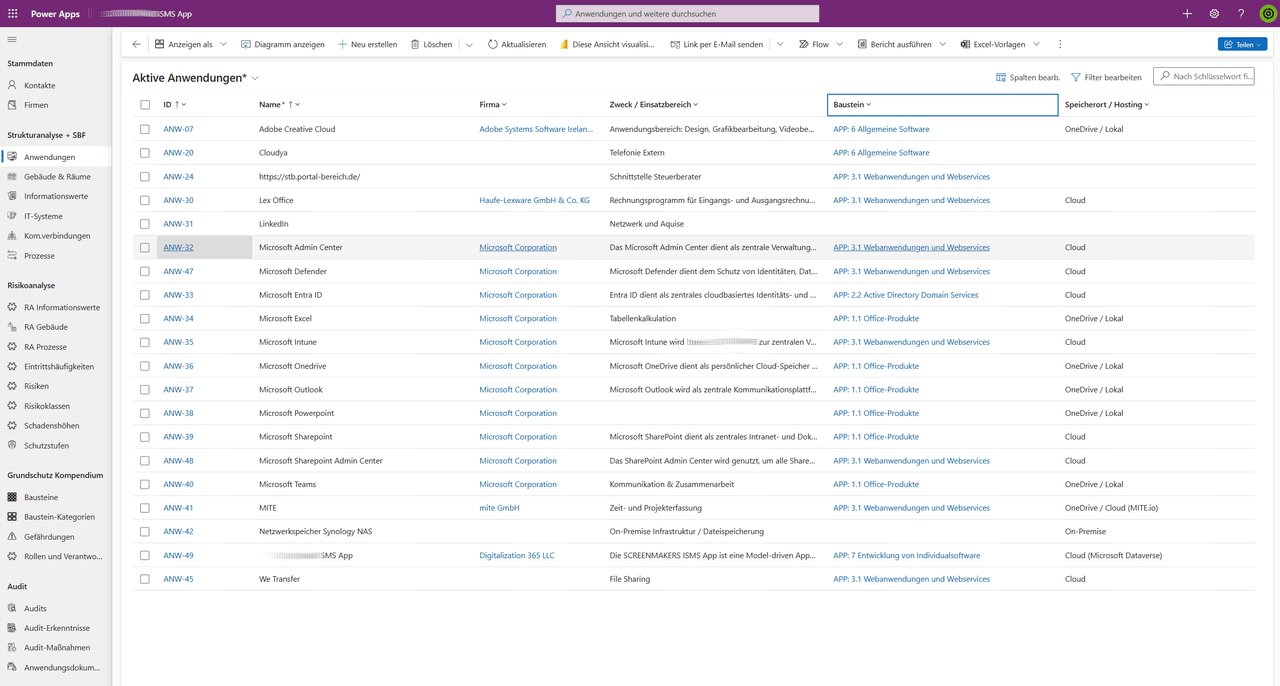 The application overview shows at a glance which protection requirements are met and where risks exist
The application overview shows at a glance which protection requirements are met and where risks exist
Power Automate and Automation: Less Manual Work
Behind the scenes, Power Automate handles repetitive, mechanical tasks. When, for example, the protection requirement classification of an information asset changes, workflows can automatically notify all dependent processes and systems and potentially recalculate associated risks. This reduces manual errors and ensures the ISMS remains consistent, even as organizational structures evolve.
Business Impact and Target Audiences
The ISMS app was purpose-built for organizations needing pragmatic, non-academic information security implementation. The target audience spans several segments: automotive suppliers required to be TISAX-compliant, mid-market companies with significant Microsoft 365 investments, IT service providers building audit foundations for their clients, and security consultants seeking a scalable ISMS implementation tool.
For the pilot organization, deploying the ISMS app had immediate business impact: time spent on risk analyses dropped by approximately 60 percent, as structured capture and automated calculation replaced manual analysis. Error rates in protection requirement assessment approached zero, since inheritance logic eliminated inconsistencies. The company gained a living, maintainable ISMS instead of a static document that became obsolete every six months.
Formulate requirements professionally
Use our Requirements Builder to create professional requirements using the SOPHIST methodology.
Technical Stack and Integration
The technical architecture is deliberately modern without being overcomplicated. Microsoft Dataverse serves as the central data repository, storing all ISMS information in normalized form. Model-Driven Apps provide the user interface—built without a single line of custom JavaScript, instead through configuration in the Power Apps designer. Power Automate supplies the automation engine. The solution integrates seamlessly into Microsoft Teams and SharePoint, so security reports and documentation can be exported directly from the ISMS.
The decision to use Microsoft Dataverse rather than build a custom database pays dividends long-term: the system runs on the same infrastructure as other Microsoft 365 applications, maintains identical security and compliance standards, and requires no separate IT maintenance. We use the same Dataverse approach for industry-specific applications like our energy management system spanning 281 power plant projects.
For organisations that take information security seriously, secure endpoints are equally important. Our zero-touch IT onboarding with Intune Autopilot ensures compliance policies apply from the very first login — a crucial building block for any ISMS.
Next Steps: How to Build a Similar System
If you're in a similar situation—you need structured information security management, you're already running Microsoft 365, but you don't want to invest in expensive external tools—then a purpose-built ISMS on the Dataverse foundation is a practical, maintainable solution. The system works particularly well if you prefer working with agile, iterative processes and would rather build your ISMS than install it off-the-shelf.
Let's discuss in a strategy call how a similar system could look for your organization—and what specific requirements you're facing.
Technology Stack:
- Microsoft Dataverse
- Power Apps (Model-Driven Apps)
- Power Automate
- Microsoft 365
- SharePoint, Teams
- Azure (optional for advanced analytics)
More Use Cases

PV Project Controlling: 281 Projects in One Dashboard
281 PV projects scattered across Excel, DATEV, and email inboxes. How an energy company gained real-time visibility into project profitability, yield, and cash flow with Power BI.
Grid Operator Billing: Processing 350 Documents Per Month Automatically
How an energy company automated the processing of 350 monthly billing documents from 11 grid operators, reducing manual work from 2–3 days to 4 hours while cutting error rates from 8% to under 1%.

Dog Training App with Power Apps
How we built a mobile-first dog training management app for a startup using Microsoft Power Apps — enabling trainers to scale their business without custom development.
Ready to automate your processes?
Book a complimentary 30-minute intro call.
No commitment, no sales pitch.